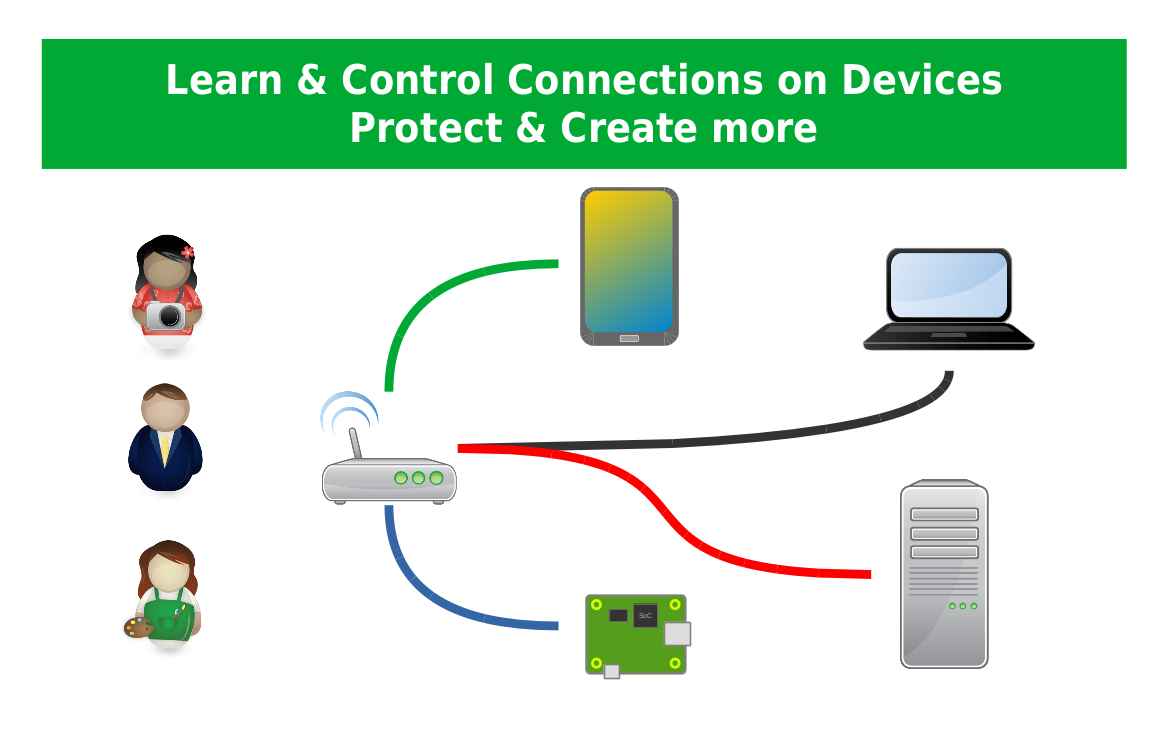
Connecting remote IoT devices securely has become a critical aspect of modern technology. With the rise of smart devices, ensuring a safe and efficient connection is essential for both personal and professional use. This article dives deep into how you can securely connect your Raspberry Pi for peer-to-peer (P2P) communication, focusing on Windows as the primary platform for downloading and setting up the necessary tools.
In today's interconnected world, IoT devices are revolutionizing the way we live and work. From smart homes to industrial automation, these devices bring convenience and efficiency to everyday tasks. However, with great connectivity comes the responsibility to ensure security. This article will guide you through the process of securely connecting your Raspberry Pi for remote P2P communication, ensuring your data remains protected.
Whether you're a tech enthusiast, a professional developer, or someone curious about IoT, this article provides valuable insights into creating a secure connection for your Raspberry Pi. We'll cover everything from setup to troubleshooting, ensuring you have all the tools and knowledge needed to succeed.
Read also:Jonathan Taylor Thomas Death Debunking The Myth And Exploring His Journey
Understanding the Basics of IoT and Raspberry Pi
What is IoT?
The Internet of Things (IoT) refers to the network of physical devices embedded with sensors, software, and connectivity that allow them to exchange data. These devices range from simple household appliances to complex industrial machines, all designed to improve efficiency and automation.
IoT devices rely on secure communication channels to function effectively. Understanding the basics of IoT is crucial for anyone looking to integrate these technologies into their projects or daily lives.
Introduction to Raspberry Pi
Raspberry Pi is a small, affordable computer that can be used for a variety of purposes, including IoT projects. It is a versatile platform that supports multiple operating systems and programming languages, making it ideal for developers and hobbyists alike.
- Raspberry Pi is known for its flexibility and ease of use.
- It supports various programming languages, including Python, Java, and C++.
- With its GPIO pins, Raspberry Pi can interface with external devices and sensors.
Why Securely Connect Remote IoT Devices?
Security is paramount when dealing with IoT devices. Without proper security measures, your devices could be vulnerable to cyberattacks, leading to data breaches and potential financial losses. Securing your IoT devices ensures that your personal and sensitive information remains protected.
Key reasons for securing IoT devices include:
- Protection against unauthorized access.
- Prevention of data breaches.
- Enhancement of overall system reliability.
Steps to Securely Connect Remote IoT P2P Raspberry Pi
Step 1: Setting Up Your Raspberry Pi
Before you can securely connect your Raspberry Pi, you need to set it up properly. This involves installing the operating system, configuring network settings, and ensuring all necessary software is installed.
Read also:Chris Rock Wife A Comprehensive Look Into Her Life Career And Relationship
Follow these steps to set up your Raspberry Pi:
- Download the latest version of Raspberry Pi OS from the official website.
- Write the OS image to an SD card using software like Balena Etcher.
- Insert the SD card into your Raspberry Pi and power it on.
Step 2: Configuring Network Settings
Once your Raspberry Pi is set up, you need to configure its network settings. This involves setting up Wi-Fi or Ethernet connections and ensuring that your device can communicate with other devices on the network.
To configure network settings:
- Access the Raspberry Pi configuration tool.
- Set up Wi-Fi by entering your network credentials.
- Verify the connection by pinging a known IP address.
Downloading Necessary Software for Windows
For users working on Windows, downloading the necessary software to connect to your Raspberry Pi is essential. This includes tools like PuTTY for SSH connections and WinSCP for file transfers.
Using PuTTY for SSH Connections
PuTTY is a popular tool for establishing SSH connections between your Windows PC and Raspberry Pi. It allows you to remotely access your Raspberry Pi's terminal and execute commands.
To use PuTTY:
- Download PuTTY from the official website.
- Open PuTTY and enter your Raspberry Pi's IP address.
- Connect and log in using your Raspberry Pi's credentials.
Using WinSCP for File Transfers
WinSCP is a secure file transfer protocol (SFTP) client that allows you to transfer files between your Windows PC and Raspberry Pi. It ensures that your file transfers remain secure and protected from unauthorized access.
To use WinSCP:
- Download WinSCP from the official website.
- Enter your Raspberry Pi's IP address and login credentials.
- Transfer files by dragging and dropping them between your PC and Raspberry Pi.
Implementing Security Measures
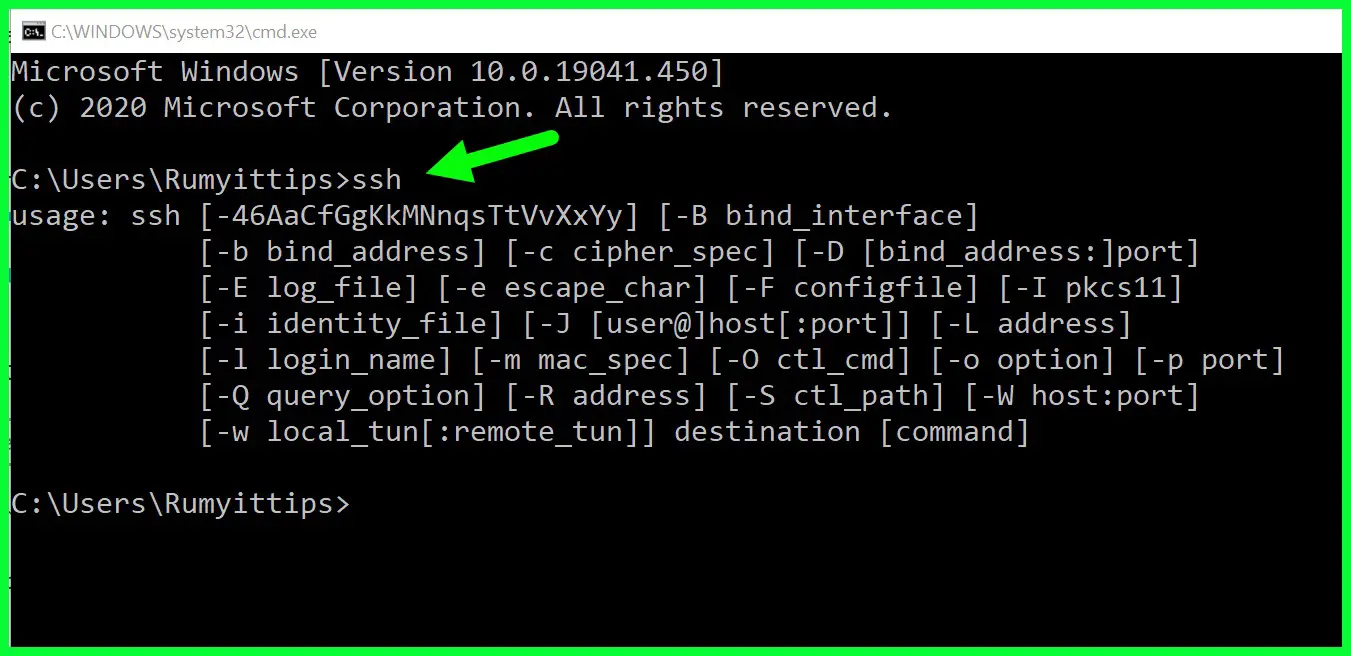
Using SSH for Secure Communication
SSH (Secure Shell) is a protocol that provides secure communication between devices over an unsecured network. It is essential for ensuring that your Raspberry Pi's communication remains encrypted and protected from eavesdropping.
To implement SSH:
- Enable SSH on your Raspberry Pi by accessing the configuration tool.
- Use tools like PuTTY to establish SSH connections from your Windows PC.
- Regularly update your SSH keys to enhance security.
Configuring Firewall Settings
A firewall acts as a barrier between your Raspberry Pi and potential threats on the internet. Configuring your firewall settings ensures that only authorized traffic can access your device.
To configure firewall settings:
- Install a firewall software like UFW (Uncomplicated Firewall) on your Raspberry Pi.
- Set up rules to allow or deny specific types of traffic.
- Monitor your firewall logs regularly to detect any suspicious activity.
Peer-to-Peer (P2P) Communication
Understanding P2P Networks
P2P networks allow devices to communicate directly with each other without relying on a central server. This type of communication is ideal for IoT devices that need to exchange data quickly and efficiently.
Key benefits of P2P communication include:
- Reduced latency compared to server-based communication.
- Improved scalability and reliability.
- Lower costs due to reduced reliance on central servers.
Setting Up P2P Communication with Raspberry Pi
To set up P2P communication between Raspberry Pi devices, you need to configure them to communicate directly. This involves setting up static IP addresses, configuring network interfaces, and ensuring both devices are on the same subnet.
Follow these steps:
- Assign static IP addresses to both Raspberry Pi devices.
- Configure network interfaces to allow direct communication.
- Test the connection using tools like ping or SSH.
Troubleshooting Common Issues
Even with careful setup, issues can arise when connecting IoT devices. Understanding common problems and their solutions can save you time and frustration.
Network Connectivity Issues
Network connectivity issues are one of the most common problems when setting up IoT devices. These can be caused by incorrect IP configurations, faulty cables, or Wi-Fi interference.
To troubleshoot network connectivity issues:
- Check your IP address settings and ensure they are correct.
- Test your network cables or switch to a different Wi-Fi network.
- Restart your router and modem to refresh the connection.
Security Configuration Problems
Security configuration problems can prevent your Raspberry Pi from communicating securely. These issues may arise from outdated SSH keys, incorrect firewall rules, or misconfigured encryption settings.
To address security configuration problems:
- Update your SSH keys regularly and ensure they are unique for each device.
- Review your firewall rules and make adjustments as needed.
- Verify that your encryption settings are up to date and comply with best practices.
Conclusion and Call to Action
In conclusion, securely connecting remote IoT devices using Raspberry Pi is a crucial step in ensuring the safety and reliability of your projects. By following the steps outlined in this article, you can set up a secure P2P connection that protects your data and enhances your device's functionality.
We encourage you to take the next step by experimenting with your Raspberry Pi and exploring the vast possibilities of IoT. Leave a comment below if you have any questions or share this article with others who may find it useful. For more in-depth guides and tutorials, explore our other articles on the website.
Table of Contents
- Understanding the Basics of IoT and Raspberry Pi
- Why Securely Connect Remote IoT Devices?
- Steps to Securely Connect Remote IoT P2P Raspberry Pi
- Downloading Necessary Software for Windows
- Implementing Security Measures
- Peer-to-Peer (P2P) Communication
- Troubleshooting Common Issues
- Conclusion and Call to Action