Remote SSH on Raspberry Pi has become an essential tool for developers and hobbyists alike, enabling seamless access and control over IoT devices. Whether you're managing a home automation system or deploying industrial solutions, understanding how to implement the best IoT device remote SSH setup is crucial. This guide will walk you through everything you need to know to optimize your Raspberry Pi for secure and efficient remote access.
IoT technology has revolutionized the way we interact with devices, and Raspberry Pi stands at the forefront of this innovation. With its affordability and versatility, Raspberry Pi has become the go-to platform for building IoT projects. However, ensuring secure remote access to these devices is critical for maintaining system integrity and privacy.
This comprehensive guide will cover everything from setting up SSH on Raspberry Pi to advanced configurations for enhanced security. Whether you're a beginner or an experienced developer, you'll find actionable insights and practical tips to enhance your IoT projects. Let's dive in!
Read also:Cowboys Fans React To Smith Rumor A Deep Dive Into The Buzz Surrounding The Dallas Cowboys
Table of Contents
- Introduction to Raspberry Pi and IoT
- What is SSH and Why It Matters for IoT?
- Setting Up SSH on Raspberry Pi
- Best Practices for Secure Remote SSH
- Advanced SSH Configurations
- Troubleshooting Common SSH Issues
- Comparison of SSH Clients for Raspberry Pi
- Automating SSH Connections
- Enhancing Security with SSH Keys
- Conclusion and Next Steps
Introduction to Raspberry Pi and IoT
Raspberry Pi has emerged as a cornerstone of IoT development, offering a compact yet powerful platform for various applications. From smart home systems to industrial automation, Raspberry Pi enables developers to create innovative solutions that connect devices seamlessly.
In this section, we'll explore the role of Raspberry Pi in IoT ecosystems and how remote SSH enhances its functionality. Understanding the basics of Raspberry Pi and its capabilities is essential for leveraging its full potential in IoT projects.
Key Features of Raspberry Pi
- Affordable hardware with versatile computing capabilities
- Support for multiple operating systems, including Raspbian and Ubuntu
- Built-in GPIO pins for interfacing with sensors and actuators
- Community-driven support and extensive documentation
These features make Raspberry Pi an ideal choice for developers looking to build scalable IoT solutions.
What is SSH and Why It Matters for IoT?
SSH, or Secure Shell, is a network protocol that provides encrypted communication between devices. In the context of IoT, SSH plays a vital role in ensuring secure remote access to devices like Raspberry Pi.
By using SSH, developers can manage and control IoT devices from anywhere in the world, provided they have an internet connection. This capability is particularly important for monitoring and maintaining systems in remote locations.
Advantages of Using SSH for IoT
- Encrypted communication for enhanced security
- Remote command execution and file transfer
- Compatibility with various operating systems
- Support for automation and scripting
These advantages make SSH an indispensable tool for IoT projects, ensuring both functionality and security.
Read also:Eddie Guerrero Cause Of Death A Comprehensive Look Into The Legacy And Tragic End
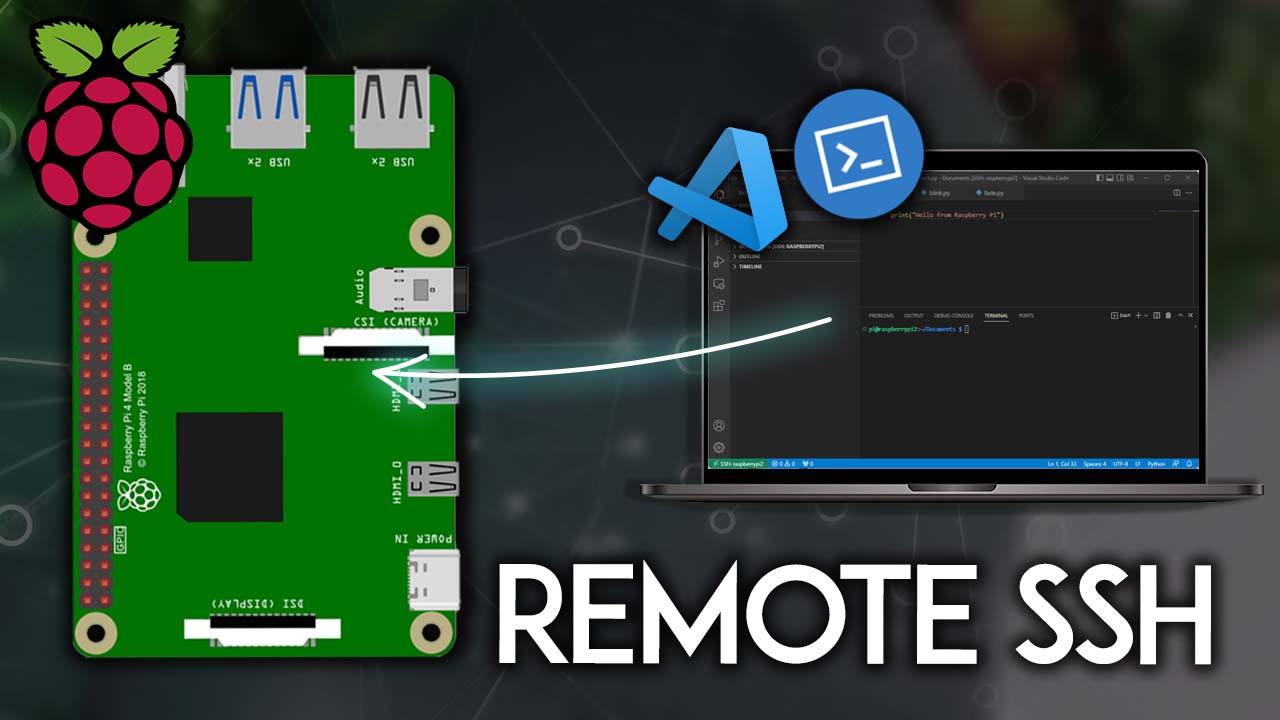
Setting Up SSH on Raspberry Pi
Configuring SSH on Raspberry Pi is a straightforward process that can be done in a few simple steps. Whether you're using a graphical interface or a command-line interface, this section will guide you through the setup process.
Step-by-Step Guide
- Install the latest version of Raspberry Pi OS on your device
- Enable SSH by navigating to the "Raspberry Pi Configuration" menu
- Set a secure password for your Raspberry Pi user account
- Connect your Raspberry Pi to a local network via Ethernet or Wi-Fi
Once SSH is enabled, you can use an SSH client to connect to your Raspberry Pi remotely. This setup forms the foundation for secure IoT device management.
Best Practices for Secure Remote SSH
While SSH offers robust security features, it's essential to follow best practices to protect your IoT devices from unauthorized access. This section outlines key strategies for enhancing SSH security.
Implementing Strong Password Policies
- Use complex passwords with a mix of letters, numbers, and symbols
- Avoid using default passwords provided by the manufacturer
- Enable password expiration to enforce regular updates
Limiting User Access
- Create separate user accounts with restricted privileges
- Use the "sudo" command for administrative tasks
- Disable root login to prevent direct access to critical system files
By adhering to these best practices, you can significantly reduce the risk of security breaches in your IoT projects.
Advanced SSH Configurations
For advanced users, customizing SSH configurations can further enhance the functionality and security of your Raspberry Pi. This section explores some advanced settings that can be implemented to optimize your SSH setup.
Configuring SSH Port Forwarding
SSH port forwarding allows you to securely tunnel traffic between devices. This feature is particularly useful for accessing services running on your Raspberry Pi from remote locations.
Enabling Two-Factor Authentication
Two-factor authentication (2FA) adds an extra layer of security to your SSH connections. By requiring a second form of verification, such as a one-time password, you can protect your IoT devices from unauthorized access.
Refer to trusted resources like SSH.com for detailed instructions on implementing advanced SSH configurations.
Troubleshooting Common SSH Issues
Even with proper setup and configuration, SSH issues can arise from time to time. This section addresses common problems users may encounter when working with SSH on Raspberry Pi and provides solutions to resolve them.
Connection Timeout Errors
- Check your network connection and ensure your Raspberry Pi is reachable
- Verify the SSH service is running on your Raspberry Pi
- Adjust the SSH timeout settings in your client software
Permission Denied Errors
- Ensure the correct username and password are being used
- Check file permissions on your Raspberry Pi
- Verify SSH keys are properly configured if using key-based authentication
By following these troubleshooting tips, you can quickly identify and resolve SSH-related issues, ensuring uninterrupted access to your IoT devices.
Comparison of SSH Clients for Raspberry Pi
There are several SSH clients available for accessing Raspberry Pi remotely. Choosing the right client depends on your operating system and personal preferences. This section compares popular SSH clients and highlights their key features.
Popular SSH Clients
- PuTTY: A widely used SSH client for Windows with a simple and intuitive interface
- OpenSSH: A command-line SSH client pre-installed on most Linux and macOS systems
- MobaXterm: A feature-rich SSH client for Windows with additional tools for remote management
Each client has its strengths, so it's important to evaluate your needs before selecting one. For detailed comparisons, refer to authoritative sources like Lifewire.
Automating SSH Connections
Automation can streamline the process of managing multiple IoT devices via SSH. By scripting repetitive tasks, you can save time and reduce the risk of errors. This section explores methods for automating SSH connections on Raspberry Pi.
Using SSH Keys for Passwordless Login
SSH keys eliminate the need for entering passwords each time you connect to your Raspberry Pi. By generating and configuring SSH keys, you can establish secure, passwordless connections.
Scheduling Tasks with Cron
Cron is a time-based job scheduler in Unix-like operating systems. By combining Cron with SSH scripts, you can automate tasks such as backups and updates for your IoT devices.
For more information on automating SSH connections, consult reliable sources like GNU.
Enhancing Security with SSH Keys
SSH keys provide a more secure alternative to password-based authentication. By using SSH keys, you can protect your IoT devices from brute-force attacks and unauthorized access.
Generating SSH Keys
- Open a terminal or command prompt on your computer
- Run the command "ssh-keygen" to generate a new key pair
- Copy the public key to your Raspberry Pi using the "ssh-copy-id" command
Disabling Password Authentication
Once SSH keys are configured, you can disable password authentication to further enhance security. Edit the SSH configuration file on your Raspberry Pi and set the "PasswordAuthentication" option to "no."
For additional security tips, refer to trusted resources like Center for Internet Security.
Conclusion and Next Steps
In this comprehensive guide, we've explored the best IoT device remote SSH solutions for Raspberry Pi. From setting up SSH to implementing advanced configurations, you now have the knowledge and tools to secure and manage your IoT projects effectively.
Remember to follow best practices and regularly update your systems to protect against emerging threats. For further reading, consider exploring topics like IoT security frameworks and cloud-based IoT platforms.
We invite you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our site for more insights into IoT and Raspberry Pi development. Together, let's build a safer and more connected future!